Introduction to VertiGIS Studio Access Control
VertiGIS Studio Access Control is a standalone, web-based product that gives you fine-grained control over who can access your ArcGIS Server services, and the layers, fields, features, geometries, and geoprocessing tasks it contains.
ArcGIS Server service permissions are limited to the service level. However, Access Control lets you control user and user group access at the layer level, the field level, and the task level.
Specifically, you can:
- Deny / allow access to an entire service.
- Control who can view and edit layers.
- Control who can view and edit fields.
- Control who can access geoprocessing tasks.
- Add filters to allow specified users/groups access to only a subset of features, based on the feature attributes. For details, see Configure Attribute Filters.
- Add filters to allow specified users/groups access to only a subset of features, based on the location of the features. For details, see Configure Geometry Filters.
- Configure JavaScript expressions to apply multiple permission rules and filters all at once. Note that this is an advanced feature. You will need a basic understanding of JavaScript to configure expressions. For details, see Advanced Permissions.
VertiGIS Studio Access Control deals with permissions only. It does not authenticate the user. Authentication still takes place through ArcGIS.
Supported Servers and Services
VertiGIS Studio Access Control is installed on the same server as your ArcGIS Server and supports the security model used to secure ArcGIS Server:
- Federated Security
- Windows Integrated Security
- Token Security
For details, see Key Concepts.
Access Control supports MapServer, FeatureServer, and GPServer services only.
Configuring Permissions in VertiGIS Studio Access Control
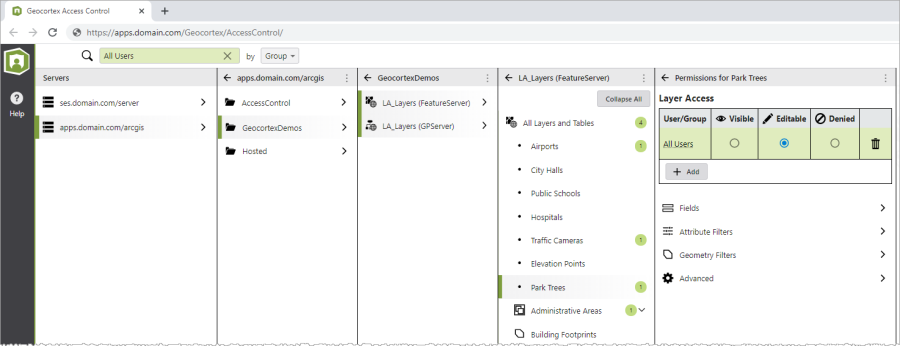
Access Control includes a web-based designer for administrative configuration. The Access Control Designer creates permissions using a behind-the-scenes RESTful configuration service. Permission configuration is transparent to end users and to client applications.
Sign in to the Access Control Designer using your ArcGIS Administrator identity. If you do not have an on-premise portal, you can sign in with your ArcGIS Online account and manage your on-premise services.
When you sign in, you will see a list of ArcGIS Servers. Some ArcGIS Servers—such as federated servers—are detected automatically, but you can also register ArcGIS Servers manually. You can register as many ArcGIS Servers as you want.
Select an ArcGIS Server to see a catalog of the folders and services on that server. You can apply permissions at the service level, or drill down to find the layer, field, or geoprocessing task on which to apply more fine-grained permissions.
- You can configure permissions for individual users and for user groups.
- You can also search for a user or group to view the permissions currently configured.
Note the following:
-
If you are denied permission to see a service in ArcGIS, you will not see it listed in Access Control Designer.
-
Unsupported services—for example, GeometryServer—are listed in the Designer, but are not available for selection.
VertiGIS Studio Access Control is an administrative tool. You should restrict access to the Designer to ArcGIS administrator users only.
How Does Access Control Work?
In a typical deployment, Access Control is installed on the ArcGIS Server and acts as a forwarding proxy for the ArcGIS Web Adaptor that is used to access ArcGIS Server.
When the client application issues a request (shown as dashed arrows in the diagram below), the following sequence of events occurs.
-
The client request is received by the ArcGIS Web Adaptor.
-
The Web Adaptor forwards the request to the VertiGIS Studio Access Control proxy.
-
The Access Control proxy examines the request and evaluates it against the permissions configured in the Access Control Designer.
- The proxy may:
- Allow the request.
- Deny the request.
- Alter the request to exclude unauthorized content.
-
If the user has permission to access the requested resource, the request is relayed to the back-end ArcGIS Server.
-
ArcGIS Server sends the response to the Access Control proxy.
- The Access Control proxy examines the response and evaluates it against the configured Access Control permissions.
- The proxy may:
- Allow the response.
- Alter the response to exclude unauthorized content.
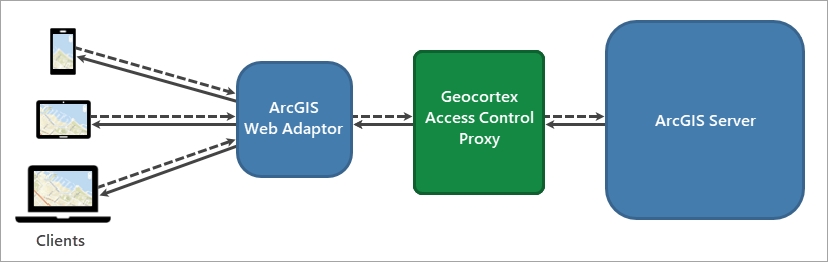
The recommended, and most common, deployment of Access Control requires ArcGIS Server to use the ArcGIS Web Adaptor. However, other deployments are also supported. For details, see Reverse Proxy and/or Load Balancer Deployments.